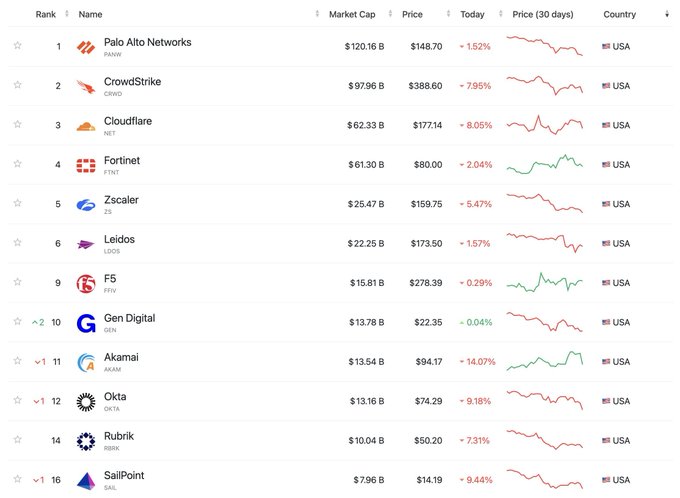
The cybersecurity market is getting hit hard on the stock market. Palo Alto Networks, CrowdStrike, Cloudflare, Zscaler, the companies that defined enterprise security for the last decade, have all been declining of late. Some are blaming macro. But the more honest explanation would seem to be structural. AI is doing what they do, faster and cheaper.
Pattern matching. Anomaly detection. Endpoint monitoring. Network threat identification. These capabilities are collapsing toward commodity. When an LLM can do in milliseconds what took a $100M security stack to do in hours, the business model breaks.
AI is compressing differentiation in traditional detection-driven security models.
Here’s the thing though: for product security, this dynamic runs in the opposite direction.
What AI Commoditizes and What It Cannot
Traditional IT security tools are fundamentally detection and response engines. They watch traffic, compare patterns against known signatures, and flag anomalies. That is valuable. It is also increasingly solvable by AI. GPT-class models can ingest logs, identify behavioral deviations, and surface threats without a purpose-built vendor in the middle.
Product security is different. You cannot AI your way to product context. Someone has to build it.
Product security is not a detection problem. It is an engineering and lifecycle governance discipline. It begins at design time, continues through release, and extends into post-market monitoring. At its core sits a structured understanding of the product itself. That structured understanding is what we mean by product context.
Product context Is a regulatory requirement, not a preference. In regulated industries, product context is not optional. It is explicitly required.
Under UN R155, manufacturers must demonstrate a Cybersecurity Management System that continuously identifies, assesses, and mitigates risks across the vehicle lifecycle.
Under FDA Section 524B, device manufacturers must provide SBOM transparency, vulnerability monitoring, and a process for post-market risk management.
Under the EU Cyber Resilience Act, manufacturers must maintain technical documentation, risk assessments, and ongoing vulnerability handling for the operational lifetime of the product.
None of these frameworks ask whether you detect a threat quickly. They require documented evidence of how the product was architected, analyzed, monitored, and maintained over time.
That documentation is product context.
What does product context mean. It means knowing what is actually inside a connected device. Every software component. Every hardware dependency. Every cryptographic library. Every interface exposed to the outside world. It means having a threat model that maps how an attacker would move through that architecture. It means understanding which vulnerabilities matter to that specific product, in that specific regulatory environment, with that specific risk posture.
That context has to be built up systematically, product by product, version by version. It requires SBOM data, architecture models, threat analysis and risk assessment outputs, compliance mappings, threat catalogs, and vulnerability history. All correlated and kept current.
AI needs that context to be useful. Without it, you’re asking an LLM to reason about threats in a vacuum.
The Context Layer Is the Moat
This is why we built EVSec the way we did. The platform’s core function is not just running security tools. It is building and maintaining a rich, living cyber model for every product in your portfolio.
Every binary we analyze, every source code scan, every SBOM we ingest, every threat we model, all of it accumulates into a product-specific intelligence layer that gets smarter over time. Our threat catalogs, attack trees, and component libraries are refined continuously. When a new CVE drops, the platform does not just flag it. It knows which of your products are affected, why, and what the downstream compliance implications are.
In regulatory audits, the question is not whether a security tool flagged an anomaly. The question is whether the manufacturer can demonstrate traceability. From architecture to threat model, to risk decision, to mitigation, to validation, and through post-market monitoring.
That traceability cannot be retrofitted by AI. It must be built into the product lifecycle.
That is what our AutoSynth AI layer runs on. Not generic training data. Your product’s actual architecture. Your threat model. Your regulatory obligations with deep domain expertise derived from accumulated data.
AI without context produces generic outputs. AI with EVSec context produces actions.
The Market Is Splitting
What we are watching happen in real time is a bifurcation of the security market.
On one side are IT and OT security tools that detect threats in running infrastructure. AI commoditizes this. Margins compress. Consolidation follows.
On the other side are product security platforms that build and maintain the intelligence layer that makes AI effective. This gets more valuable as AI becomes more central to security operations. The better the context, the better the AI.
For regulated industries including automotive, medical devices, and industrial systems, this distinction is existential. A CVE that slips through an IT security stack is a bad day. A CVE that slips through a connected medical device or vehicle ECU, is a product recall, an FDA enforcement action, or worse. The compliance obligations under UN R155, FDA 524B, and the EU Cyber Resilience Act demand exactly the kind of deep product context that AI cannot generate on its own.
In these environments, cybersecurity is not simply a best practice. It is tied to market access, product approval, and ongoing regulatory supervision.
When a vulnerability surfaces, regulators and notified bodies expect evidence. Which product versions are affected. Which functions are exposed. What risk decisions were made. How mitigation actions were validated.
AI can accelerate analysis. It cannot reconstruct historical accountability.
What This Means Going Forward
The companies declining in that market cap table were built on detection. AI owns detection now.
C2A Security is built on context and domain expertise. The richer the context, the more powerful the AI that runs on top of it. That is a flywheel, not a commodity trap.
For our customers in automotive, medical devices, industrial, and IoT, this is the moment to get ahead of it. The manufacturers who build robust product security intelligence now will not just survive the AI transition. They will be the ones who use it to outrun their competition.
The static compliance tools are getting commoditized too. The platforms that convert product intelligence into dynamic compliance systems are where value is concentrating.
AI will reshape how security work is executed. It will not change what regulators require manufacturers to prove.
The manufacturers who build structured product intelligence today will be the ones who withstand audit scrutiny tomorrow.
That is what we are building.
Contact us to learn more.