Providing Contextual Insights Tailored to Your Infrastructure
Jerusalem, Israel, April 3, 2025: C2A Security, the only context-driven product security orchestration platform that addresses the specific needs of software-defined products and cyber-physical systems, announced today a major step forward in how product security teams analyze and respond to cyber threats at scale by introducing a new Context-Based Threat Intelligence Module (product).
This new addition enhances the company’s product security platform, EVSec, by automating the process of analyzing raw threat data, giving product security teams and executives the context, clarity, and speed needed to tackle real-time risks more effectively. Unlike traditional vulnerability scanning, the Threat Intelligence Module automatically extracts threat activities – including Zero-Day vulnerabilities – to provide contextual insights tailored to your infrastructure, with AI-based enrichment adding depth to the data.
Ransomware attacks have been a well-known threat vector to medical organizations for several years, peaking during the pandemic and again in 2023 and 2024, resulting in extensive downtime for organizations. A recent study by IBM showed that organizations took an average of 194 days to identify a data breach and 292 days to contain it – with the average cost of downtime being around $1.9 million per day.
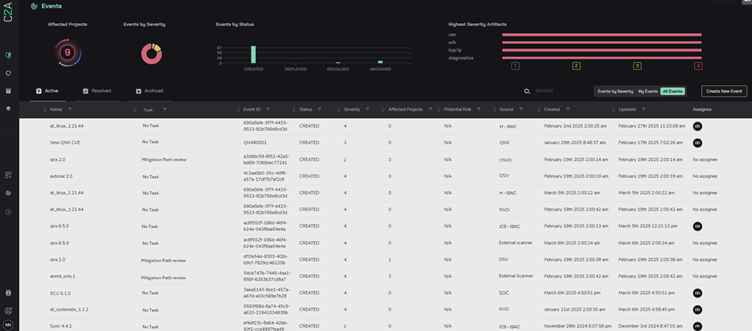
The new Threat Intelligence Module leverages multiple sources of threat data, including the Internet, dark web, ISAC reports, and social media platforms, to automatically create actionable security events. Powered by AutoSynth AI, the company’s novel AI-based infrastructure layer, the new Threat Intelligence Module accelerates vulnerability management and post-production threat analysis by seamlessly integrating with known threat intelligence sources like Health-ISAC and Auto-ISAC reporting.
“In today’s rapidly evolving threat landscape, time is of the essence. The medical sector has seen devastating impacts from cyber threats and ransomware attacks – often with downtime costs in millions of dollars. The new Threat Intelligence Module is designed to address this critical gap”, said David Mor Ofek, Head of Product, C2A Security. “With AI-driven insights, C2A Security’s contextualized approach gives teams the clarity and speed to respond effectively, reducing the average response time and potential damage. Integrating with community and industry platforms like ASRG, Health-ISAC, and Auto-ISAC ensures you’re always equipped with the most relevant threat data to protect your products.”
Key Features of the Threat Intelligence Module:
- Automated Threat Intelligence Analysis: Automatically analyze raw threat intelligence sources and generate security events to identify potential risks earlier.
- Integration with Known Threat Sources: Ingest and correlate data from trusted threat intelligence sources, such as Health-ISAC, Auto-ISAC, and other sources, along with public and private vulnerability databases such as NVD, OSV, C-NVD, and Qualcomm, ensuring your defense mechanisms are always updated with the latest threat data.
- Post-Production Vulnerability Management: Track vulnerabilities throughout the product lifecycle, from development to deployment, ensuring ongoing protection.
- Manage the Threat Analysis, Prioritization, and Mitigation Process: Assign tasks, track progress, and gain product insights to guide your team’s response to emerging threats. Automate triage processes and generate actionable remediation recommendations based on AI-enhanced risk analysis.
How It Works:
EVSec collects threat data from various sources, including the dark web, white-hat researchers, security blogs, GitHub, white papers, and social media. This intelligence is analyzed by the AutoSynth AI layer, which converts the data into actionable security events. The Threat Intelligence Module then evaluates these events based on their relevance to your product, context-driven, ensuring only high-impact threats are processed.
The C2A Advantage: Context-Driven Threat Intelligence
While other companies offer threat intelligence solutions primarily focusing on scanning events, C2A Security provides contextualized security insights. Linking raw data with your specific products through EVSec enables you to not only detect threats but also understand their impact on your infrastructure and how to best mitigate them.
This approach gives your team the relevant context to act quickly and efficiently, minimizing the time from threat identification to mitigation.
Schedule a demo today to experience the new Context-Based Threat Intelligence Module in person and improve your organization’s response time to emerging threats.